DMARC (Domain-based Message Authentication, Reporting & Conformance) is an email authentication protocol. It is used to protect email senders and recipients from email spoofing, which is the practice of sending emails with a forged sender address.
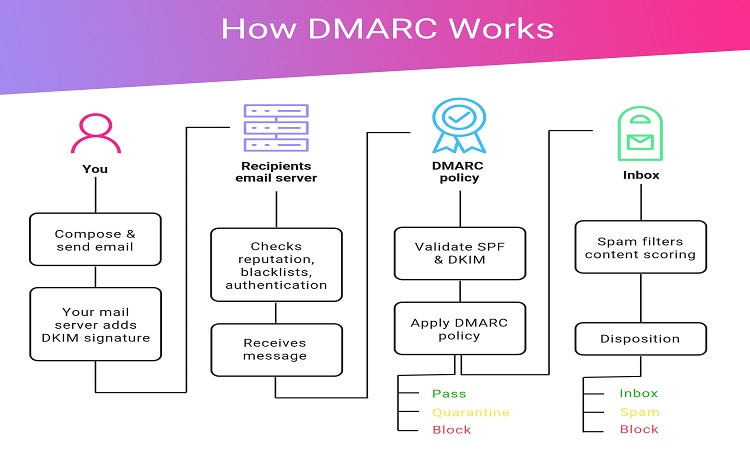
DMARC works by allowing the email sender’s domain to publish a policy specifying which mechanisms (such as SPF and DKIM) should be used to authenticate email messages sent from that domain.
Email receivers can then check if the incoming messages comply with the sender’s policy and take appropriate action, such as marking the message as spam or rejecting it. DMARC helps to improve email security and protect users from phishing and other email-based attacks.
DMARC can be improved in several ways:
Adoption:
The first step to improving DMARC is to increase its adoption among email senders and receivers. Encouraging more organizations to implement DMARC can lead to better protection against email spoofing and phishing attacks.
Alignment with SPF and DKIM:
DMARC works best when used in conjunction with SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail). Both of these protocols help to authenticate email messages, and aligning them with DMARC can lead to a more robust and effective email authentication system.
Monitoring and enforcement:
DMARC policies need to be monitored and enforced to be effective. Regular monitoring of email traffic to ensure compliance with DMARC policies can help to identify any issues and prevent email spoofing.
Regular updates:
DMARC policies should be updated regularly to keep up with evolving email security threats.
Public reporting:
DMARC includes a reporting mechanism that can be used to gather data on the use and enforcement of DMARC policies. This data can be used to identify trends and make informed decisions about how to improve DMARC.
Final Word
Implementing these improvements can lead to a stronger, more effective DMARC system, and help to protect against email-based attacks.

